Christian Rap Lives
 This is a cross-post from the blog of Vitamin Z, where I am guest-blogging this week.
This is a cross-post from the blog of Vitamin Z, where I am guest-blogging this week.
Here are five great Christian rap songs. This post comes to you ex nihilo. I have no reason for writing it, other than my love for these songs.
1. Cross Movement, “Closer to You.” This one is off the Holy Culture album. When the album came out six or so years ago, I played this song over and over. It’s got a gorgeous hook by JR, a hard beat by DJ Official, and strong verses from all contributors. Many of us grew in the faith and in love for hip-hop because of CM, so it’s fun to reflect back on their work.
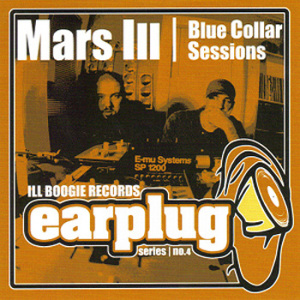
2. Mars Ill, “Two Steps.” Coming from the Blue Collar Sessions ep, which is very hard to find and very good. Manchild (formerly soulHEIR the Manchild) is a poet, and this beat by Dust fits his pitch-perfect, low-varnish flow elegantly. Three great stories told in this song, a very different kind than the first. I heard this song and thought (perhaps delusionally), “I want to do that.” It was a Tina Fey-kind of moment that led to world tours, mansions, and dinner conversations with Prince. Sorry, that last bit was
…
Recent Comments